tiCrypt
End-to-End Encrypted Compute Environments
A single, fully integrated platform for regulated workloads designed to exceed NIST 800-171/CMMC Level 2 requirements.
NIST 800-171/CMMC Level 2 Compliant
NIST 800-172/CMMC Level 3 Ready
Are you an Academic Organization?
See how tiCrypt supports secure research workflows, regulated data collaboration, and high-performance computing environments.
Is tiCrypt a Good Fit for Your Organization?
A simple four-point check to help determine whether tiCrypt aligns with your compliance, infrastructure, and deployment needs.
Fit & alignment
Four Questions
Does your organization handle regulated workflows (e.g., NIST SP 800-171/172, CMMC Level 2 or 3, ITAR)?
Are your workflows dependent on software outside Microsoft 365 that cannot run in GCC High?
Does your organization have the scale and resources to operate an on-premises secure environment?
Is your organization based in the United States or Canada?
Alignment Score
Begin by answering each question.The score indicates whether your organization aligns with the conditions tiCrypt is designed to support.
No responses are stored, logged, or transmitted. Processed locally within your session.
Compliance
SSP Coverage (NIST 800-171 / CMMC Level 2)
tiCrypt provides a complete SSP blueprint (110 controls). Approximately 84 controls are platform-enforced (including hybrid controls where tiCrypt enforces the technical component). The remaining ~26 controls are organizational and require customer-specific policy edits (e.g., PE, AT, PS, and policy-driven areas).
tiCrypt Core Features
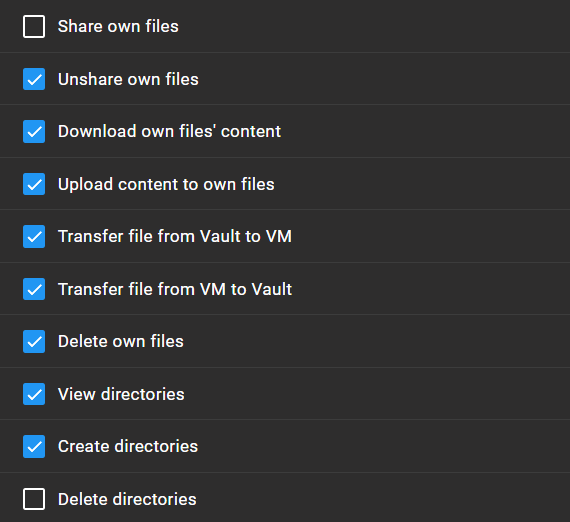
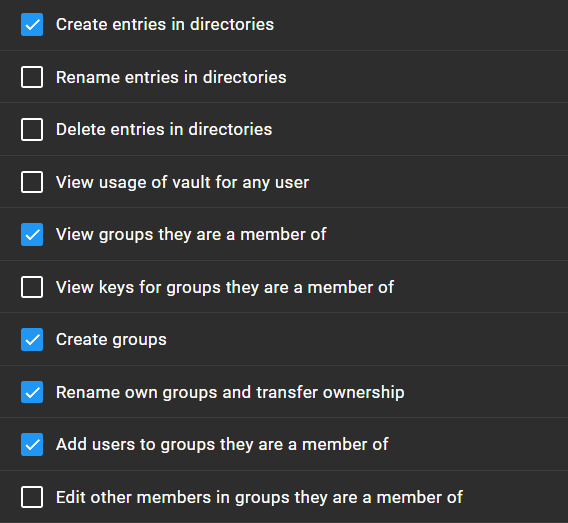
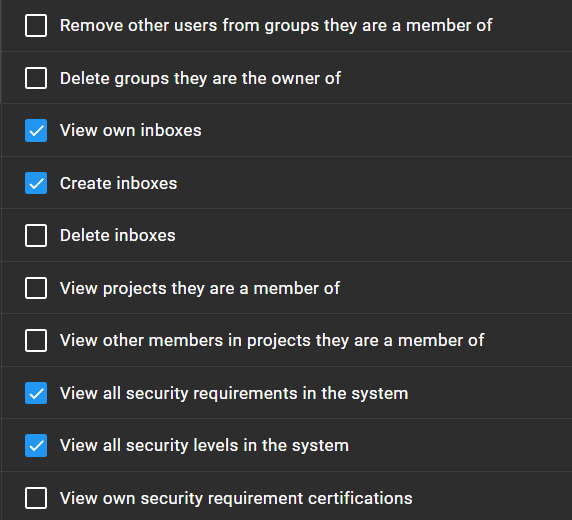
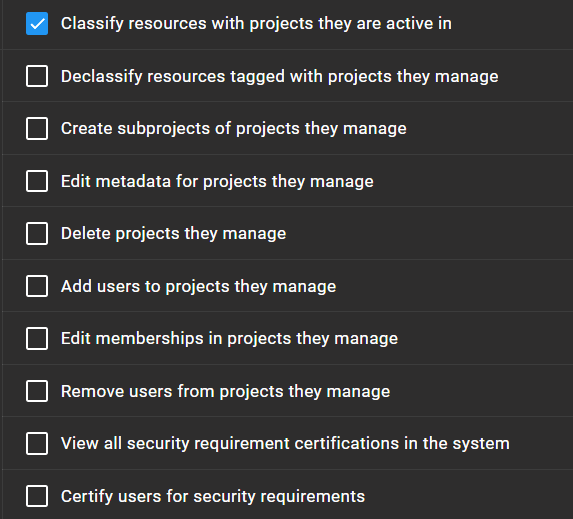
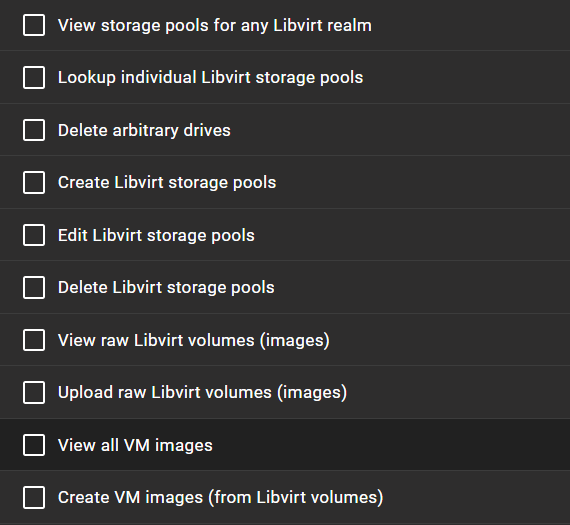
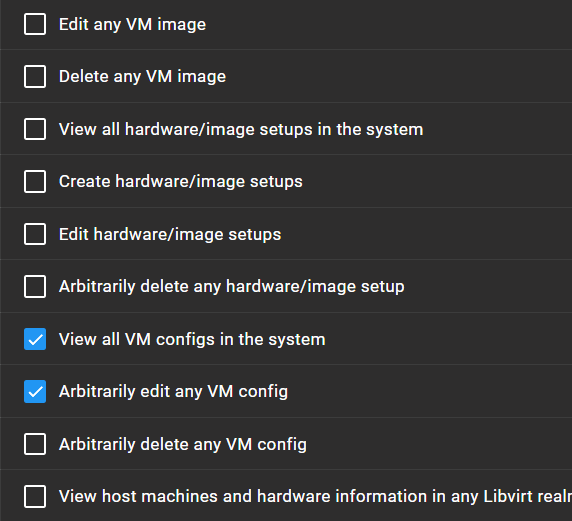
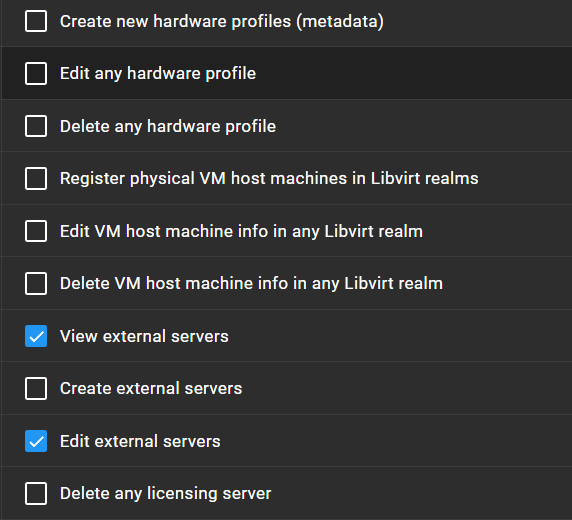
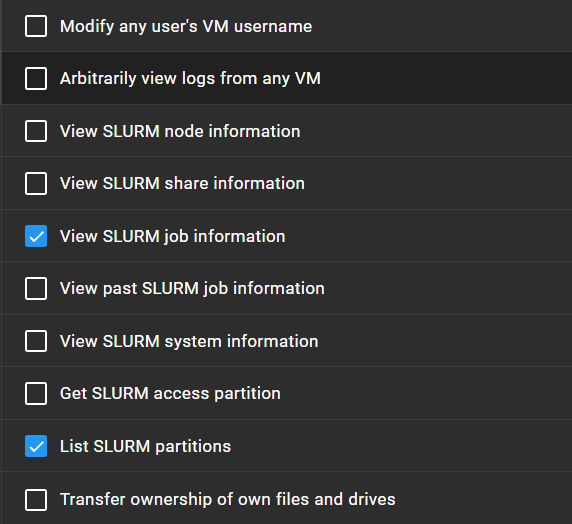
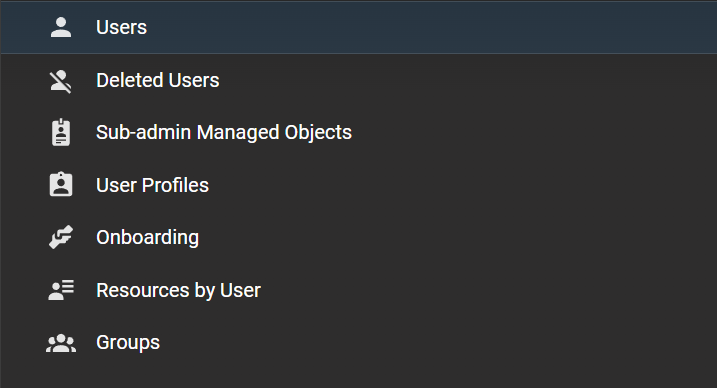
Core features include a secure Vault for file storage and sharing, controlled access to virtual machines via RDP and terminal sessions, and integrated administrative tools for managing users, permissions, and system activity.
- RSA-2048 key pairs are generated at registration, and the private key never leaves the user.
- All authentication is based on digital signatures, not stored credentials.
User-Centric PKI
tiCrypt provides end-to-end encryption for file access, sharing, and processing, with a security model built on public-key cryptography. Every user holds their own RSA-2048 key pair, while all drives, files, and data are end-to-end encrypted with AES-256. Administrators cannot access user data unless it is explicitly shared with them.
- AES-256 encryption is managed through PKI for every file and drive.
- Without the decryption key, stored data is useless, even to administrators.
- Secure key recovery is handled through multi-party approval.
Virtual Machines
Encrypted Virtual Machines
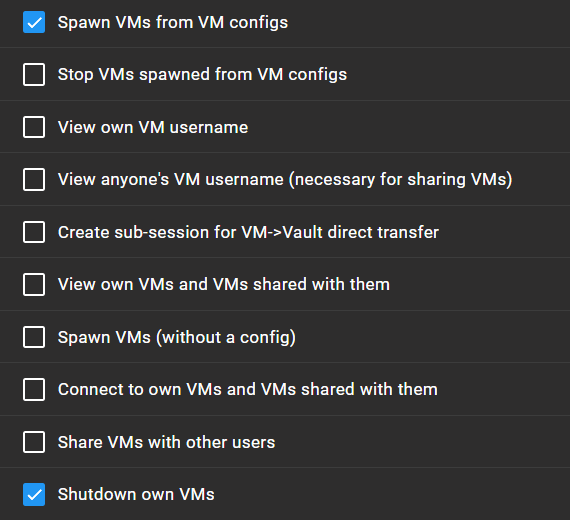
tiCrypt runs computation inside isolated Linux, Windows, clustered, and batch-processing VMs with encrypted storage, controlled networking, and full session auditing.
- VM drives are encrypted with LUKS or BitLocker, with keys held by the data owner.
- The control channel uses WebSockets into the backend, encrypted and authenticated by digital signature.
- Backend services and administrators have no access to VM contents.
- Stand-alone, clustered, and batch-processing VM configurations support a wide range of workloads without complex remote access tooling.
Compliance
Compliance Built Into the Architecture
tiCrypt enforces encryption, isolation, audit logging, and reporting at the platform level, reducing reliance on manual procedures and lowering operational overhead for regulated environments handling CUI, ITAR, and FISMA-driven workloads.
- CMMC 2.0 Level 2 certified.
- NIST 800-171 certified.
- FIPS 140-3 compliant cryptography.
- Built-in audit reporting and system monitoring.
- Reduced compliance burden through controls enforced by design.
Secure HPC with Split-Instance SLURM
tiCrypt separates HPC scheduling from execution using split-instance SLURM. A global SLURM instance handles resource allocation and accounting, while local per-project SLURM instances execute jobs inside secure VMs against data and code available only within the authorized project environment.
- Global SLURM handles resource allocation and accounting through a service account.
- Local SLURM runs per project inside secure VMs, executing jobs against data and code available only within that authorized environment.
- Secure VMs become nodes integrated into the local SLURM cluster.
- Scheduling and execution are separated so the global instance never sees user data.
- SLURM job submission, interactive compute, and controlled data ingestion happen from secure environments.
Management
Multi-Organization Management
tiCrypt provides a unified platform for managing users, projects, data, access, audit, and collaboration across departments and organizations, reducing the need for complex, multi-tool environments.
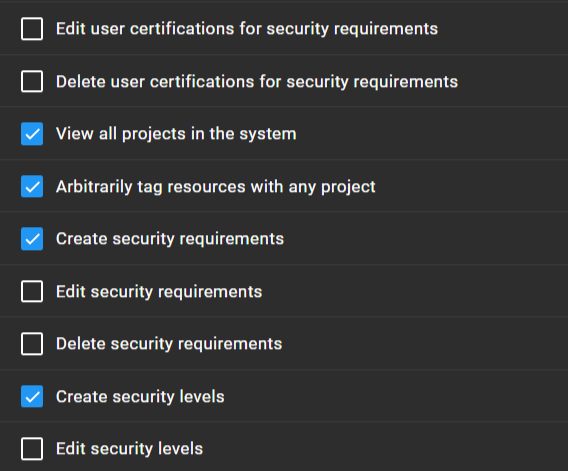
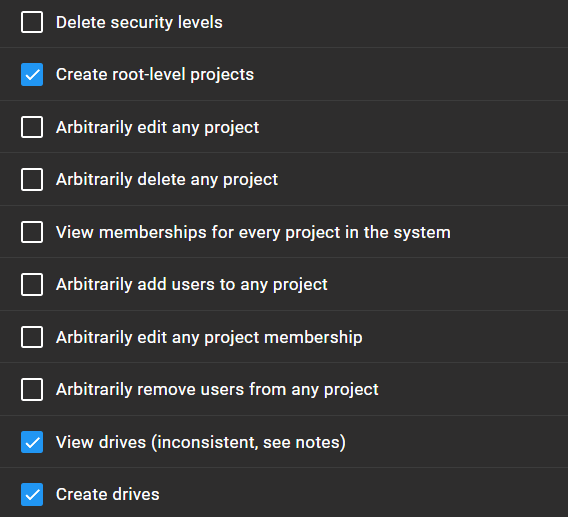
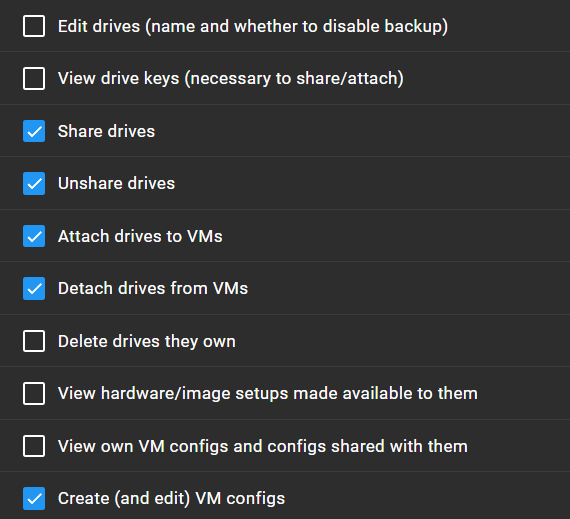
- Role-based delegation lets system administrators focus on infrastructure while project leads manage their own users and activities.
- Seamless SSO authentication supports collaboration across multiple organizations.
- Every operation is tracked through centralized logging and monitoring, creating a full audit trail.
- RPM-based deployment supports existing on-premises or cloud bare-metal infrastructure.
What Our Customers Say About tiCrypt
Why tiCrypt?
tiCrypt is a single-stack solution designed for secure, compliance-ready data processing at scale.
tiCrypt vs Traditional In-House Solutions
A side-by-side comparison highlighting operational, security, and compliance differences.
Learn More
Explore our resources to better understand tiCrypt and CMMC-aligned secure compute environments.
- For an overview of system architecture and features, see Architecture and Features.
- To learn how we integrated SLURM, see HPC.
- Why we plan to integrate Common Access Cards (CAC), see CAC.
- To watch videos of the system in action, see Demo.
- To learn about licensing, support, and pricing, view Pricing.
- To learn more about our SSP blueprints, visit SSP.
- To learn more about our company, visit About.